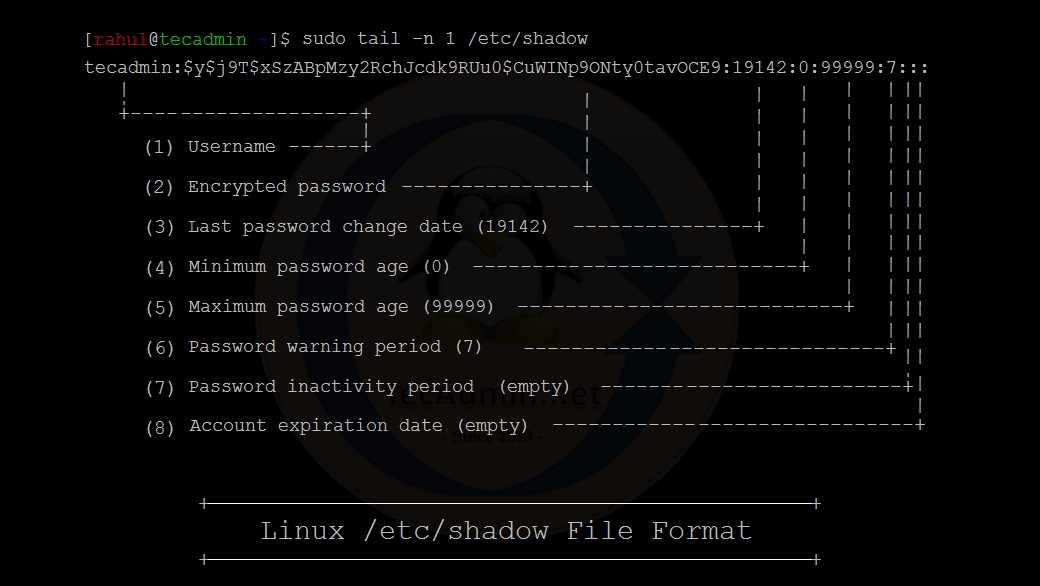
The /etc/shadow file contains one line for each user account, with the fields being separated by a colon (:). The below screenshot shows the number of fields in an entry:
A basic overview of all the fields in the /etc/shadow file is as follows:
Username: The name of the user account. Encrypted password: The encrypted password for the user account. The encrypted password is stored using a one-way hashing function, so it is not possible to retrieve the original password from the encrypted version. The initial letters of the encrypted password tell about the encryption methods used to create the password. $1$: MD5 $2a$: Blowfish $2b$: Blowfish $2y$: Blowfish $5$: SHA-256 $6$: SHA-512 $y$: Yescrypt Last password change (date): The date on which the user last changed their password, represented as the number of days since January 1, 1970. Minimum password age: The minimum number of days that must pass before the user is allowed to change their password again. Maximum password age: The maximum number of days that the user’s password is valid before it must be changed. Password warning period: The number of days before the user’s password is set to expire that the user will receive a warning. Password inactivity period: The number of days of inactivity after which the user’s password will expire and the account will be locked. Account expiration date: The date on which the user’s account will be disabled, represented as the number of days since January 1, 1970.
Note that the /etc/shadow file is only readable by the root user, so it is not possible for normal users to view the contents of this file or to retrieve the encrypted passwords of other users.
How to Update /etc/shadow File
Before we begin, it is important to note that modifying the /etc/shadow file should be done with caution, as any mistakes can potentially compromise the security of user accounts on the system. It is recommended to make a backup of the /etc/shadow file before making any changes.
Conclusion
In this article, you have learned about the /etc/shadow file in a Linux system. You know about the detail of the fields in a single entry of the shadow file. Along with that, you got to know about password aging in Linux.
To replace the password of the other user account, we can use the following command:
Replace USERNAME with the name of the user whose password you want to set up aging for. Replace NUMBER_OF_DAYS with the number of days you want the user’s password to remain valid. For example, if you want the user’s password to expire after 90 days, you would use the command: This command will set the maximum password lifetime to 90 days and the password expiration warning period to 7 days. Once you have set up the password aging rules, you can check the status of the user’s password with the following command: This command will give you information about the user’s password, including when it will expire and the maximum password lifetime.